Why tokenization programs stall
Ex-Post compliance is a regulatory liability
When transfers execute first and get checked later, every non-compliant transaction creates permanent, auditable evidence of a policy violation on an immutable ledger. This is not a technical inconvenience. It is a regulatory and reputational liability.
Institutions operating across multiple jurisdictions face compounding complexity: different eligibility rules, different investor classifications, different holding restrictions. Without automated, pre-execution enforcement, compliance teams become the bottleneck — or worse, violations slip through.
Transfers Execute Before Validation
Most platforms check compliance after the transfer. The result: immutable on-chain evidence of policy violations that boards and regulators will not tolerate.
Jurisdictional Complexity
Operating across EU MiCA, Singapore MAS, UK FCA, Japan FSA, and US Reg D/S/CF means different rules per asset, per jurisdiction, per investor type. Manual mapping is error-prone.
Manual Review Doesn't Scale
Compliance teams manually reviewing every transfer cannot scale beyond pilot volumes. At production scale, manual gates become bottlenecks that block legitimate investors.
how dalp solves it
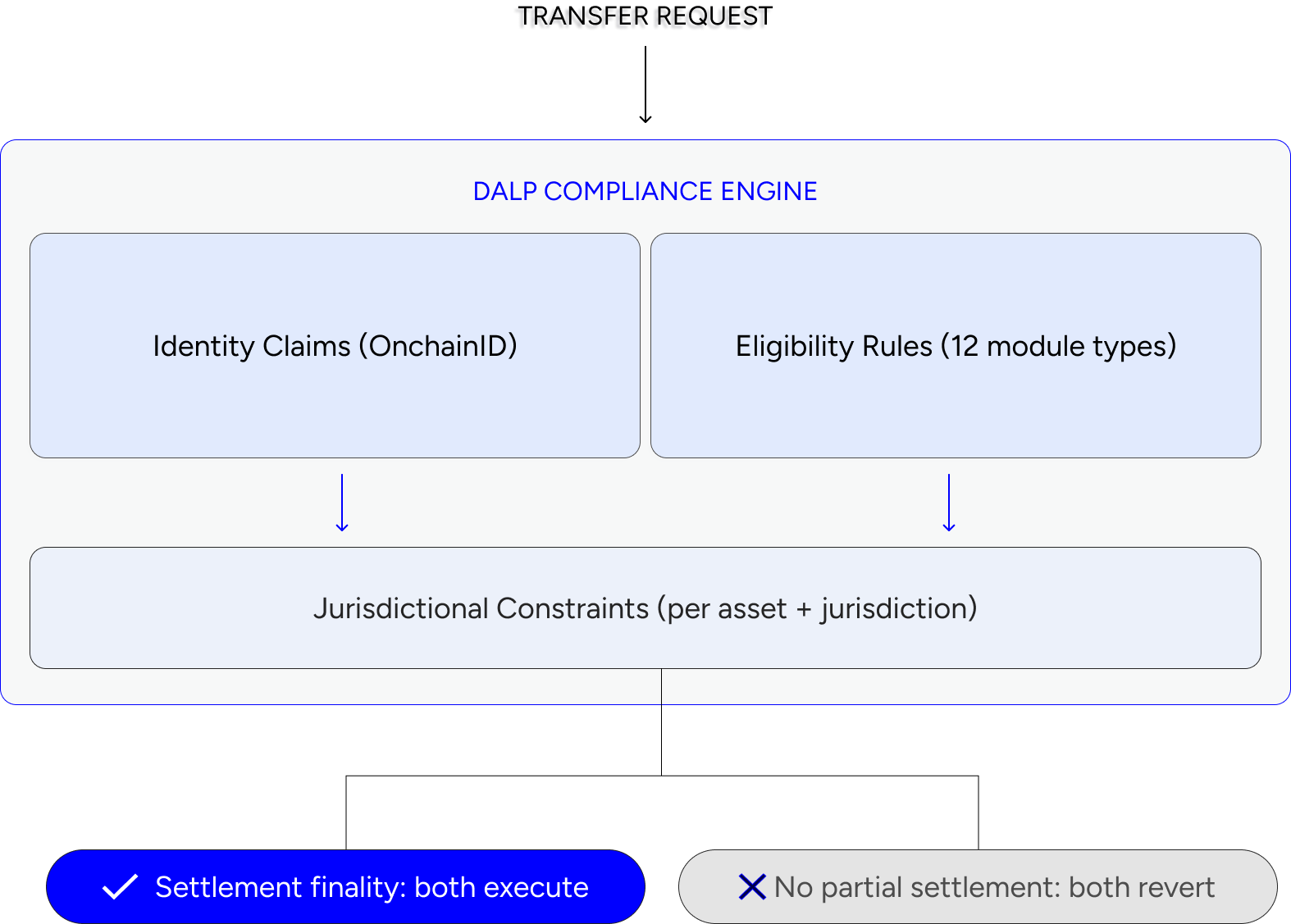
Ex-ante enforcement. Validated before execution.
Each module type is composable per asset and per jurisdiction. Rules enforce automatically — no manual review gates. Define once, apply across every transaction involving that asset and jurisdiction.
flexible setup
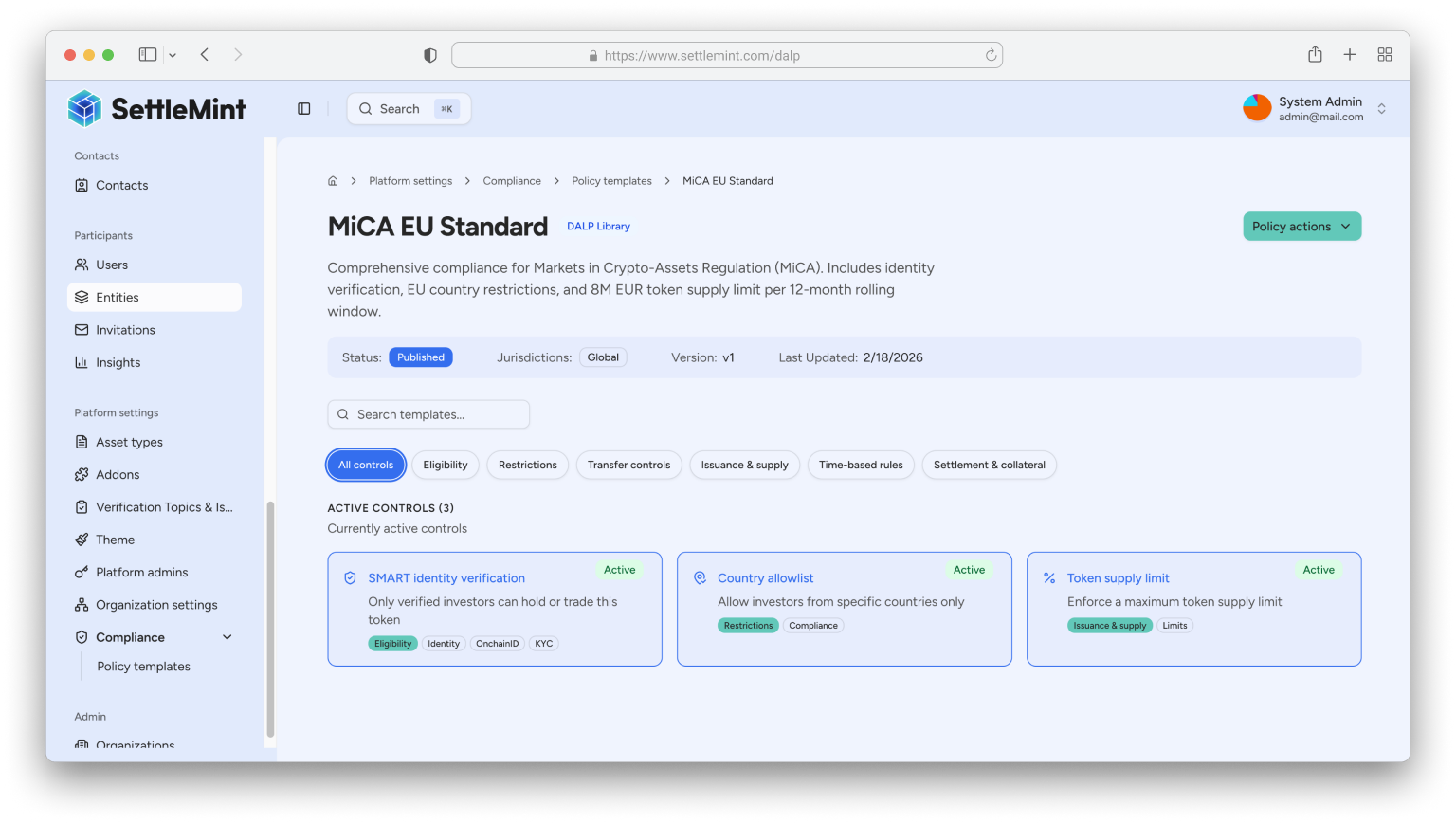
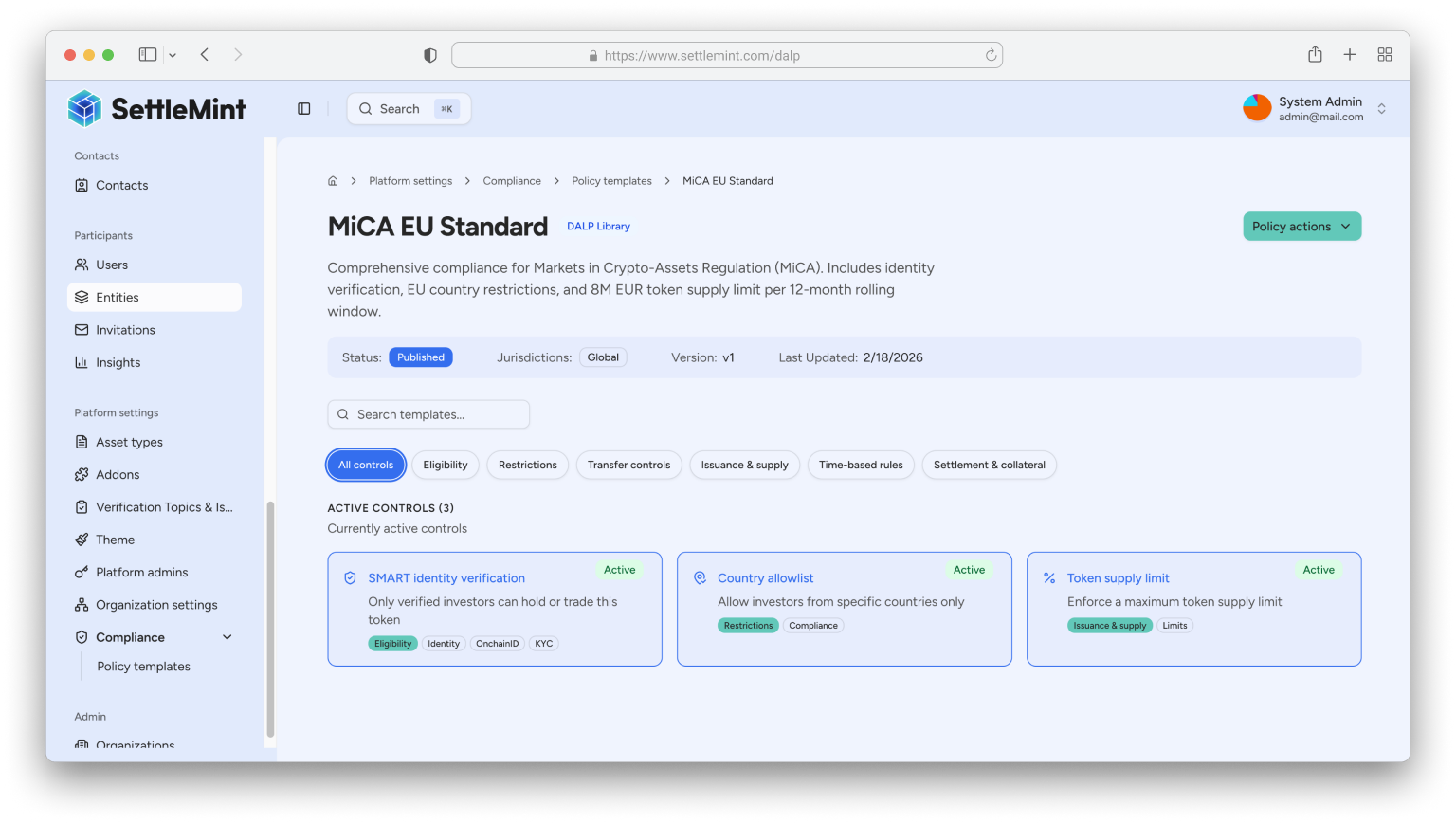
Configurable for any regulatory framework
Jurisdictional compliance templates encode the specific rules each regulatory framework requires. When an asset operates across jurisdictions, DALP composes the relevant module sets automatically. Add a new jurisdiction by configuring its template — not by rewriting compliance logic.
Identity layer: OnChainID & ERC-3643
OnChainID
OnChainID
Onboard Once
Onboard Once
ERC-3643
ERC-3643
OnChainID
OnChainID
Onboard Once
Onboard Once
ERC-3643
ERC-3643
Everything you need to issue
KYC/AML Integration
DALP does not perform KYC checks itself. It enforces claims issued by external identity providers — integrating with your existing KYC/KYB providers and encoding their verification results as on-chain identity claims.
The compliance engine validates four key claims before every transfer. Exception handling follows a deterministic remediation loop: rejected transfers include explicit reject reasons, request-update actions, and fulfillment closure on reviewed resubmissions.
Identity Verified
Claims from trusted issuers confirm KYC/KYB status
Accredited
Accreditation claims checked against asset requirements
Eligible Jurisdiction
Country claims validated against allow/block lists
Holding Period Met
Time-based restrictions enforced automatically
Compliance evidence & audit trail
Every compliance decision — approval, rejection, exception — is recorded with immutable audit evidence. The platform provides:
-
Queryable action history for compliance decisions and identity events.
-
Full evidence of checks and approvals embedded in the same system that executes transfers.
-
SIEM-ready audit logging for enterprise security integration.
-
Statistical reporting with aggregated compliance posture metrics.
-
Regulators and auditors access a single source of truth — not four databases with no unified view.
Everything you need to issue
Key Capabilities
DALP does not perform KYC checks itself. It enforces claims issued by external identity providers — integrating with your existing KYC/KYB providers and encoding their verification results as on-chain identity claims.
The compliance engine validates four key claims before every transfer. Exception handling follows a deterministic remediation loop: rejected transfers include explicit reject reasons, request-update actions, and fulfillment closure on reviewed resubmissions.
Enforcement Model
Ex-ante. Validated before execution, not reviewed after
Module Types
12 configurable compliance modules
Jurisdictions
EU MiCA, US Reg D/S/CF, Singapore MAS, UK FCA, Japan FSA, GCC
Identity Standard
OnChainID with claim-based verification
Token Standard
ERC-3643 (T-REX) — open, regulated token standard
KYC/AML
Claims from external providers enforced on every transfer
Audit Trail
Immutable, queryable, SIEM-ready
Exception Handling
Deterministic remediation with reject reasons and resubmission
Everything you need to issue
Key Capabilities
DALP does not perform KYC checks itself. It enforces claims issued by external identity providers — integrating with your existing KYC/KYB providers and encoding their verification results as on-chain identity claims.
The compliance engine validates four key claims before every transfer. Exception handling follows a deterministic remediation loop: rejected transfers include explicit reject reasons, request-update actions, and fulfillment closure on reviewed resubmissions.
Enforcement Model
Ex-ante. Validated before execution, not reviewed after
Module Types
12 configurable compliance modules
Jurisdictions
EU MiCA, US Reg D/S/CF, Singapore MAS, UK FCA, Japan FSA, GCC
Identity Standard
OnchainID with claim-based verification
Token Standard
ERC-3643 (T-REX) — open, regulated token standard
KYC/AML
Claims from external providers enforced on every transfer
Audit Trail
Immutable, queryable, SIEM-ready
Exception Handling
Deterministic remediation with reject reasons and resubmission
