The Problem
Custody below enterprise grade is an existential risk
Digital asset custody is where institutional confidence lives or dies. Single-key setups, basic multi-signature without enterprise governance, and custody providers without formal recovery procedures are non-starters for risk committees at regulated institutions.
Yet most tokenization platforms either force you onto a single custody provider, offer basic key management without enterprise workflows, or, worse, try to become a custodian themselves without the licensing and operational maturity to back it.
Single-Key Risk
Single-key or basic multi-sig without HSM support or formal recovery procedures. Key loss is permanent and unacceptable to any risk committee.
No Enterprise Governance
No maker-checker approvals. No formal recovery procedures. No configurable quorum. No separation of duties. Risk committees cannot approve this.
Vendor Lock-In
Custody solutions that force you onto a single provider create dependency risk and eliminate negotiating leverage. Your assets are locked into infrastructure you don't control.
how dalp solves it
Key Guardian: multi-backend key management
Key Guardian supports multiple storage backends. Choose the security model that fits your risk framework: Connect once, reuse across every asset type. No per-asset custody integration.
Encrypted Database
Dev and test environments
Cloud Secret Manager
AWS, GCP, Azure secret stores
HSM
Hardware security modules for highest assurance
Fireblocks
Third-party institutional custody
DFNS
Third-party MPC custody
Additional Providers
Bring your own custodian. DALP orchestrates, it doesn't replace
flexible setup
Bring your own custodian
DALP is explicitly not a custodian. It does not hold keys, does not take custody of assets, and does not require a custody license. Instead, DALP provides the orchestration layer that enforces custody policy across your existing custodian relationships.
Integrate with Fireblocks, DFNS, or future providers through standard connectors
Custody policy applies consistently across all integrated providers
No forced vendor migration. Your existing custodian stays in place
Add or change custody providers without re-architecting the platform
Enterprise governance workflows
Maker-Checker Approvals
Maker-Checker Approvals
Every sensitive operation requires independent approval before execution.
Multi-Sig Quorum
Multi-Sig Quorum
Configurable quorum thresholds for high-value operations and critical actions.
5 RBAC Roles
5 RBAC Roles
Defined roles govern access from token issuance to transfer approval to system governance.
Emergency Pause
Emergency Pause
Platform-scoped emergency controls to halt operation when required.
Formal Recovery
Formal Recovery
Identity recovery after wallet loss or compromise. Staged, confirmed, auditable.
Full Audit Logging
Full Audit Logging
Every custody action logged with immutable evidence for audit and regulatory reporting.
Everything you need to issue
Vault provisioning
DALP manages the logical provisioning of custody vaults as system addons. DALP controls logical and on-chain provisioning and governance boundaries. Off-chain custody hardware and partner-run operational key ceremonies remain the custodian's responsibility.
Role-gated factory registration with identity binding
Deterministic deployment with on-chain identity association
Projection bootstrap for vault telemetry and observability
Full audit trail from provisioning through operational lifecycle
Wallet verification & transaction signing
Multi-factor verification gates protect privileged transaction signing and sensitive recovery operations.
Deterministic outcomes with auditable evidence
Revocation semantics for compromised credentials
Exclusive execution for transaction signing under concurrent load
Integrated with the platform's identity and compliance layers
Key capabilities
Everything you need to issue
Key Capabilities
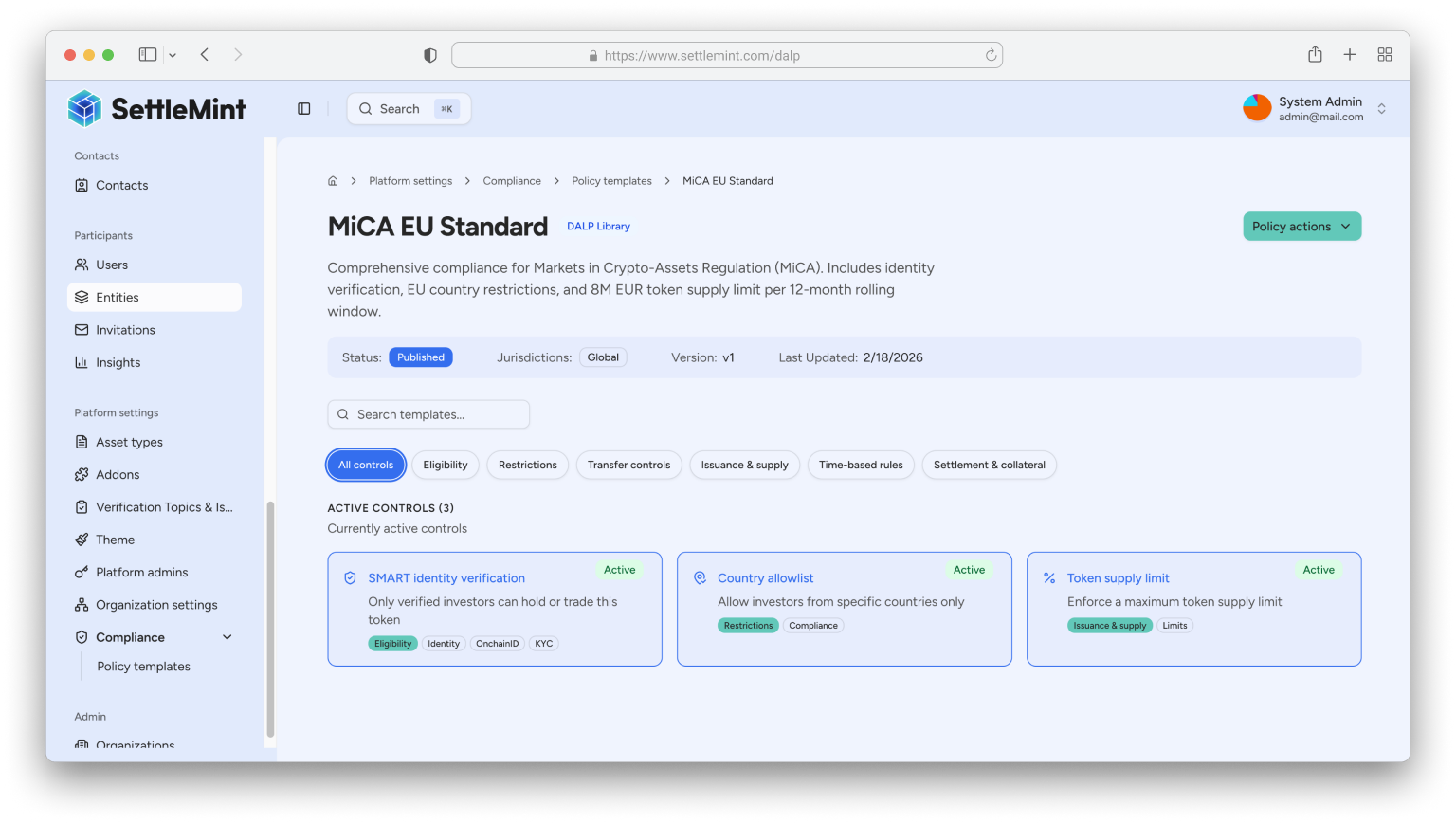
DALP does not perform KYC checks itself. It enforces claims issued by external identity providers — integrating with your existing KYC/KYB providers and encoding their verification results as on-chain identity claims.
The compliance engine validates four key claims before every transfer. Exception handling follows a deterministic remediation loop: rejected transfers include explicit reject reasons, request-update actions, and fulfillment closure on reviewed resubmissions.
Enforcement Model
Ex-ante. Validated before execution, not reviewed after
Module Types
12 configurable compliance modules
Jurisdictions
EU MiCA, US Reg D/S/CF, Singapore MAS, UK FCA, Japan FSA, GCC
Identity Standard
OnchainID with claim-based verification
Token Standard
ERC-3643 (T-REX) — open, regulated token standard
KYC/AML
Claims from external providers enforced on every transfer
Audit Trail
Immutable, queryable, SIEM-ready
Exception Handling
Deterministic remediation with reject reasons and resubmission
